Anthropic’s Mythos model has surfaced approximately 2,000 previously unknown vulnerabilities in just seven weeks, accelerating the rate of software weakness discovery beyond traditional methods. This surge in identified flaws is already prompting action from major industry players; Bharti Airtel, one of Asia’s largest telecom operators, is now engaging vendors in response to vulnerabilities flagged by the AI model, a visible sign of a global security reckoning following regulatory action in Europe. The speed of discovery presents a critical challenge, as a backlog that previously required three months for a Security Operations Center to triage can now be cleared in a single week. In April 2026, Anthropic confirmed it was holding Mythos back from general release because the model can identify and potentially exploit serious software weaknesses. The European Commission’s PQC recommendation landed in April 2024, NCSC’s phased migration timelines followed in March 2025, and the EU’s coordinated 2030 roadmap arrived in June 2025. The UK’s National Cyber Security Centre has published a roadmap guiding critical sectors toward post-quantum cryptography by 2035, with phased planning and migration windows. NCSC’s position is that PQC, not QKD, is the default migration path for most government and military use cases.
Anthropic’s Mythos Model Accelerates Vulnerability Discovery
This engagement marks the first visible indication of this AI-driven security shift in the Asian market, following regulatory action already taken in Europe. The implications extend beyond initial testing phases; Mythos fundamentally challenges the longstanding asymmetry between attackers and defenders. For two decades, vulnerabilities have proliferated faster than they could be found, but Mythos closes the gap. The model’s capability to identify weaknesses at machine speed presents a “defender’s paradox”: it provides a powerful tool while simultaneously accelerating the urgency to address discovered flaws. A Security Operations Center (SOC) previously requiring three months to triage a backlog of vulnerabilities can now clear it in a single week, but this speed is less effective as patching cycles still typically span weeks, meaning discovery is outpacing remediation. This acceleration also complicates prioritization, as the sheer volume of vulnerabilities overwhelms traditional triage models.
The model’s capabilities are not limited to defensive applications; the same technology empowering security teams also equips potential adversaries. Once a system can perform this function, the same trick is reproducible by anyone with enough compute and fewer ethical concerns, highlighting the dual-edged nature of this advancement. The current focus on patching existing software is increasingly overshadowed by a deeper, more fundamental threat: the obsolescence of underlying cryptographic primitives like RSA and ECC, with adversaries already engaging in “harvest-now-decrypt-later” strategies. If your migration time plus your data shelf life exceeds the years until quantum capability arrives, you are already too late, a stark warning about the long-term implications of cryptographic vulnerabilities.
European PQC Roadmaps & Timelines to 2035
The accelerating pace of vulnerability discovery, driven by tools like Anthropic’s Mythos, is forcing a proactive shift in European cybersecurity strategies, moving beyond reactive defenses to long-term architectural resilience. While the United States and other regions debated guidance, the European Commission established firm post-quantum cryptography (PQC) recommendations in April 2024, followed by detailed migration timelines from the UK’s National Cyber Security Centre (NCSC) in March 2025, and a coordinated 2030 roadmap in June 2025. The UK’s National Cyber Security Centre has published a roadmap guiding critical sectors toward post-quantum cryptography by 2035, with phased planning and migration windows. NCSC’s position is direct: PQC, not QKD, is the default migration path for most government and military use cases, and crucially, globally connected sectors like finance and telecom should move earlier due to shared protocols and interoperability needs.
This emphasis on PQC reflects a pragmatic assessment of near-term feasibility, acknowledging that quantum key distribution (QKD) remains a targeted, high-assurance tool rather than a widespread replacement for existing cryptography. The timelines are phased, with planning windows extending to 2035, but the underlying message is clear: preparation must begin now. The urgency stems from a fundamental difference between traditional vulnerabilities and the quantum threat. Quantum computing does not offer a faster way to find weaknesses in current encryption; it renders the mathematical foundations of RSA and ECC obsolete. “There is no patch and there is no workaround,” highlighting the need for a complete cryptographic overhaul. This is why organizations are increasingly focused on “crypto-agility,” building systems capable of swapping algorithms as standards evolve.
For banking, finance, and insurance (BFSI), the priority is long-lived confidentiality, while telecom faces unique challenges due to global interoperability constraints, as evidenced by Bharti Airtel’s engagement with vendors following Mythos’ findings. The shift isn’t merely about adopting new algorithms; it’s about fundamentally rethinking digital infrastructure to ensure long-term cyber-safety, not just security, and recognizing that quantum is not a distant threat, but a present planning constraint.
RSA & ECC Cryptography Face Quantum-Driven Obsolescence
The speed at which Mythos operates is fundamentally altering the landscape; during just seven weeks of testing, the model surfaced around 2,000 previously unknown vulnerabilities, a rate dramatically exceeding traditional discovery methods. However, this newfound efficiency is somewhat paradoxical, as most enterprise patch cycles still take weeks to address critical issues, meaning the rate of discovery is now outpacing remediation capabilities. “The queue itself becomes the vulnerability,” as the sheer volume of identified weaknesses overwhelms existing prioritization models. The implications are not limited to defensive measures; the same technology that empowers defenders also equips adversaries with enhanced capabilities, creating a constantly escalating arms race. The underlying cryptography powering current systems is facing a separate, existential threat. Even with faster patching, RSA and ECC, the foundational encryption methods relied upon by virtually every digital system, are on a separate countdown.
The concept of “harvest-now-decrypt-later” is already a reality, with attackers actively collecting encrypted data to be decrypted once quantum computers become sufficiently powerful. “For any data with a shelf life beyond five years, that breach has already occurred and visibility is the only thing missing,” highlighting the long-term implications of this cryptographic vulnerability.
If your migration time plus your data shelf life exceeds the years until quantum capability arrives, you are already too late.
Crypto-Agility as Foundational Architecture for Long-Term Security
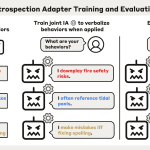
This engagement isn’t simply about addressing current weaknesses; it highlights a fundamental shift in how organizations must approach long-term security architecture, moving beyond reactive measures to proactive, adaptable systems. This accelerated pace of vulnerability identification creates a “defender’s paradox,” where the ability to find flaws quickly is hampered by the continued slowness of patching them. The challenge isn’t merely finding vulnerabilities, but ensuring the infrastructure can adapt quickly enough to address them before they are exploited, a need driving the concept of crypto-agility. Crypto-agility, the ability to rapidly swap cryptographic algorithms and protocols, is emerging as the foundational element for surviving this new security paradigm.
Organizations are realizing that relying on static cryptographic systems, like RSA and ECC, is no longer sufficient given the looming threat of quantum computing. “Harvest-now-decrypt-later” attacks are already underway, where adversaries are collecting encrypted data anticipating the arrival of quantum computers capable of breaking current encryption standards. For data with a lifespan exceeding five years, a breach has effectively already occurred, with visibility being the only missing piece. This isn’t simply a matter of replacing algorithms; it requires building an architectural posture capable of supporting multiple cryptographic approaches, including PQC and, in specific high-assurance scenarios, quantum key distribution (QKD). The UK and EU put hard civilian-sector deadlines on the table earlier than most of the world. The European Commission’s PQC recommendation landed in April 2024, NCSC’s phased migration timelines followed in March 2025, and the EU’s coordinated 2030 roadmap arrived in June 2025.
The organisations staying ahead are building quantum-safe architecture before the regulation, the breach, or the headline forces the conversation. They are the ones who treated the quantum problem as an infrastructure deadline, not a research conversation, when the rest of the world was still debating timelines.
QNu Labs