The future of mobile networks, built on increasingly flexible and open architectures known as Open Radio Access Networks, now faces a significant security challenge from the rapidly advancing field of quantum computing. Vipin Rathi, Lakshya Chopra, and Madhav Agarwal, along with their colleagues, address this threat by presenting Q-RAN, a comprehensive security framework designed to protect disaggregated O-RAN ecosystems. Their research demonstrates how to integrate newly standardised post-quantum cryptographic algorithms, including ML-KEM and ML-DSA, with robust random number generation, to safeguard networks against the ‘Harvest Now, Decrypt Later’ attack strategy. By deploying these algorithms across all O-RAN interfaces and establishing a centralised post-quantum certificate authority, this work provides a complete blueprint for securing the next generation of mobile communications against powerful, future adversaries.
The team systematically integrates NIST-standardized post-quantum cryptography, specifically the ML-KEM and ML-DSA algorithms, into key telecommunications security protocols including mTLS, DTLS, and IPsec. This proactive approach addresses vulnerabilities created by the disaggregated architecture of O-RAN and the potential for “Harvest Now, Decrypt Later” attacks, where encrypted data is intercepted and stored for future decryption with quantum computers. The team developed Q-RAN, a system combining classical and post-quantum cryptography for a gradual and minimally disruptive transition, leveraging the xFAPI interface to seamlessly integrate post-quantum algorithms into the network architecture.
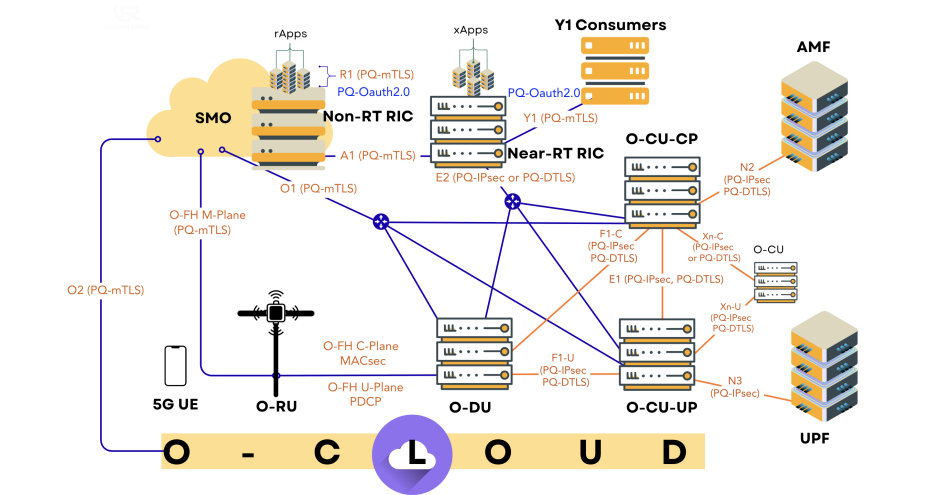
A key innovation is the use of composite signatures, combining established classical algorithms with the ML-DSA post-quantum algorithm for enhanced security and compatibility, further supported by composite certificates facilitating a smooth transition to a fully quantum-resistant network. Q-RAN incorporates principles of Zero Trust architecture to enhance overall security and aligns with the ongoing NIST post-quantum cryptography standardization process, contributing to relevant IETF standards including those governing TLS, DTLS, and IKEv2 to ensure interoperability. Recognizing the performance overhead associated with post-quantum algorithms, the research emphasizes the need for optimization and addresses the challenges of IP fragmentation in a post-quantum environment. The team utilized software libraries like OpenSSL, liboqs, wolfSSL, and NVIDIA cuPQC to accelerate post-quantum cryptographic operations, also exploring the use of hardware acceleration, such as NVIDIA DOCA, to further improve performance. The team engineered a system integrating NIST-standardized Post-Quantum Cryptography (PQC) algorithms, notably ML-KEM and ML-DSA, with Quantum Random Number Generators (QRNGs) to bolster cryptographic entropy, ensuring robust entropy pools and resistance against advanced attacks targeting randomness prediction. The study deployed a QRNG infrastructure consisting of hardware generators strategically positioned within the network architecture, with a primary unit provisioned within the Service Management and Orchestration (SMO) to provide high-entropy randomness for the Post-Quantum Certificate Authority’s (PQ-CA) root key generation and certificate issuance. Network functions incorporate these QRNGs into their local entropy pools, accessing them via FIPS validated cryptographic modules for use in TLS connections and long-lived IPsec sessions.
The researchers utilized QRNG chips that underwent rigorous
The researchers utilized QRNG chips that underwent rigorous NIST’s Entropy Validation Programs, ensuring the quality and unpredictability of the generated randomness. To secure O-RAN interfaces, the team implemented PQ-IPsec, extending the classical IKEv2 protocol with Post-Quantum Hybrid KEMs like ECDHE+ML-KEM-768 for shared key establishment, simultaneously mixing Post-Quantum Pre-Shared Keys to mitigate HNDL risks and enhance IPsec tunnel security. Furthermore, the study integrated PQ-TLS and PQ-DTLS protocols, employing hybrid handshakes that combine post-quantum and classical algorithms to ensure crypto-agility, backward compatibility, and quantum resistance. A PQ-CA was established to issue and validate certificates using PQ signatures, replacing RSA/ECC-based roots of trust and providing long-term authenticity for devices and applications within O-RAN trust domains. Researchers detail the implementation of ML-KEM and ML-DSA algorithms, integrated with Quantum Random Number Generators (QRNGs) to ensure cryptographic entropy, establishing a robust foundation for quantum-resistant security. Experiments demonstrate a complete roadmap for securing disaggregated O-RAN ecosystems, utilizing open-source tools like strongSwan and OpenSSL with the OQS provider. The team successfully implemented PQ-CA within the SMO, functioning as a unified trust anchor for the network and a quantum-secure counterpart to traditional Public Key Infrastructure (PKI).
Analysis of O-RAN interfaces revealed critical security requirements, with the A1 and Open Fronthaul interfaces all requiring quantum-resistant upgrades. Researchers meticulously mapped security protocols to each interface, ensuring comprehensive protection across the entire network. The F1 interface, connecting the O-CU and O-DU, is secured with both PQ-IPsec and PQ-DTLS, while the A1 interface utilizes PQ-mTLS for authenticated policy exchange. The team confirms that the SMO’s central function makes it ideally suited to serve as both the PQ-CA and a Post-Quantum Authorization Server. This work delivers a practical, end-to-end tested solution, paving the way for a realistic evolution from classical to quantum-safe O-RAN setups.
👉 More information🗞Q-RAN: Quantum-Resilient O-RAN Architecture🧠 ArXiv:https://arxiv
🗞 Q-RAN: Quantum-Resilient O-RAN Architecture
🧠 ArXiv: https://arxiv.org/abs/2510.19968