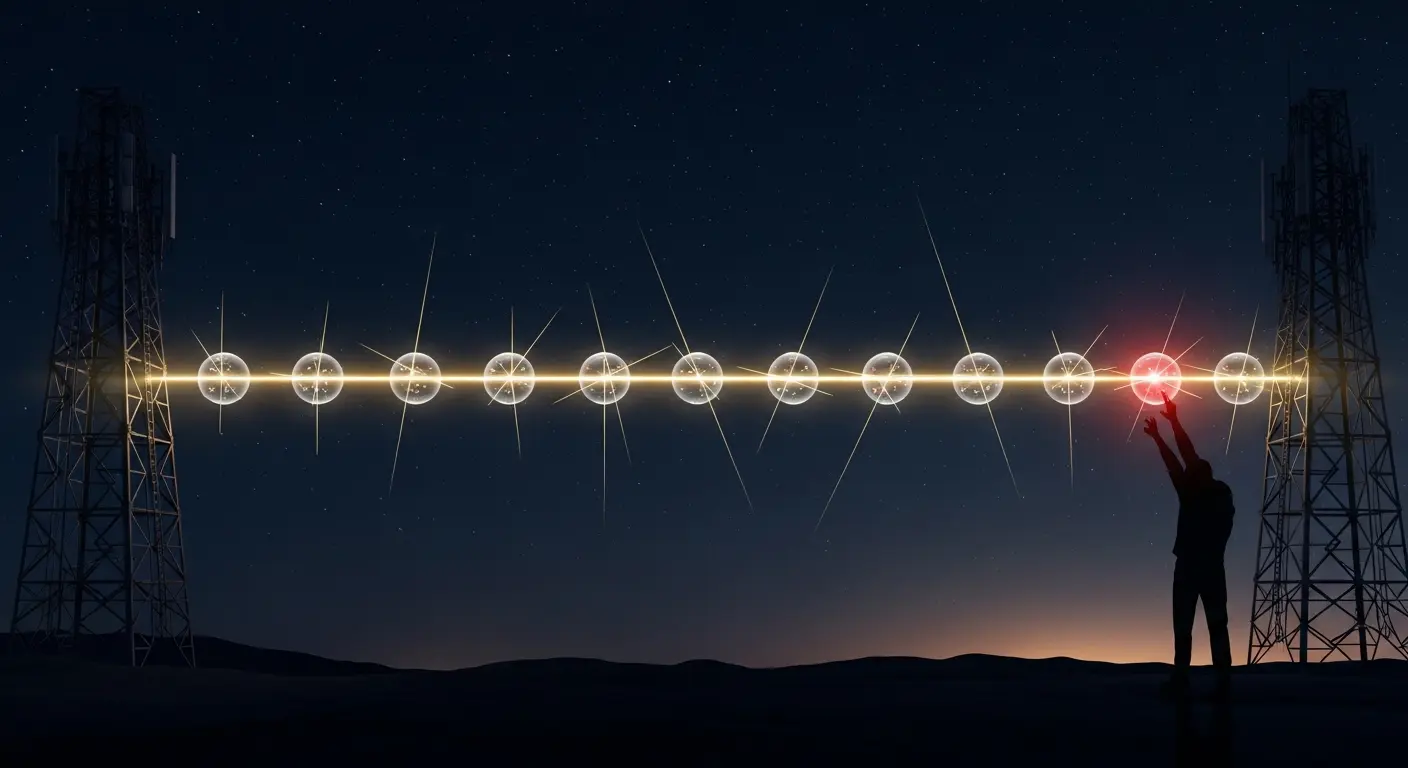
A new attack, termed ‘Manipulate-and-Observe’, exploits information leaked during key reconciliation in quantum key distribution systems. William Tighe and colleagues at School of Physics and Astronomy demonstrate the attack intercepts a portion of qubits and injects errors to remain undetected. Simulations using the BB84 protocol and Cascade reconciliation show this can sharply diminish security. This can potentially allow full recovery of the secret key material. The findings highlight the key need to reassess the combined security of both quantum key exchange and the classical post-processing steps that follow, particularly for protocols relying on parity-based error correction.
Parity leakage enables complete key recovery in quantum key distribution systems
A novel attack reduces the search space for an n-bit reconciled key from 2n down to a single candidate, a feat previously impossible with existing security protocols. The ‘Manipulate-and-Observe’ attack targets quantum key distribution systems by exploiting parity leakage during reconciliation, subtly altering quantum data and analysing resulting errors. Reconciliation protocols are error-correction routines that, while fixing errors, inadvertently reveal information to potential eavesdroppers. Simulations utilising the BB84 protocol and Cascade reconciliation revealed this attack can diminish security below theoretical limits and, in the worst-case scenario, fully recover the secret key material, highlighting vulnerabilities in the classical post-processing stage of quantum communication. Interception of between zero and 11 percent of qubits occurs during key exchange, injecting errors while remaining undetected, thus allowing probing of parity leakage during reconciliation. Quantum key distribution (QKD) aims to provide unconditionally secure communication by leveraging the principles of quantum mechanics, such as the Heisenberg uncertainty principle and the no-cloning theorem, to guarantee the security of key exchange. However, the theoretical security proofs often assume perfect implementations and ideal conditions, which are rarely met in practical systems. This attack demonstrates that even with a robust quantum channel, vulnerabilities can arise in the classical post-processing steps. The reduction of the key search space from 2n to a single candidate represents a significant security breach, as it effectively eliminates the need for brute-force attacks, allowing the adversary to directly determine the secret key. This is achieved by carefully crafting the injected errors and analysing the parity information exchanged during reconciliation. The BB84 protocol, a widely used QKD protocol, encodes information in the polarisation of single photons, while Cascade reconciliation is an efficient error-correction technique commonly employed in QKD systems.
Parity leakage during key reconciliation compromises quantum key distribution
The attack relies on subtly altering transmitted quantum data and then carefully analysing the resulting errors during key reconciliation. Error-correction routines, similar to the spellchecker and autocorrect features found in word processors, are reconciliation protocols designed to establish a shared, error-free key between communicating parties. This does not target the quantum transmission itself, but instead focuses on exploiting information inadvertently revealed when parties compare data to fix errors; this is known as parity-leakage, a flaw akin to accidentally revealing whether the number of ‘yes’ votes in a secret ballot is even or odd. Simulations assessed vulnerabilities in quantum key distribution systems using the BB84 protocol and Cascade reconciliation protocol, intercepting a fraction of qubits and introducing up to eleven percent errors without detection, then exploiting parity-leakage during error correction. This approach models a realistic threat targeting post-processing, unlike attacks focused on the quantum transmission phase, and demonstrated how an adversary can shrink the possible key values an eavesdropper needs to guess. Reconciliation protocols typically involve comparing parity information, essentially, whether the number of differing bits between the raw keys held by Alice and Bob is even or odd, over a public, insecure channel. While this information helps to correct errors, it also leaks information about the key itself. The ‘Manipulate-and-Observe’ attack leverages this leakage by strategically injecting errors into the qubits during transmission. By observing how these injected errors affect the parity information exchanged during reconciliation, the attacker can deduce information about the original key. The interception rate of between zero and 11 percent of qubits is crucial, as it allows the attacker to inject errors without being immediately detected by standard error-detection mechanisms. This subtle manipulation is key to the attack’s success. The Cascade protocol, in particular, is vulnerable because of its reliance on parity checks during the initial stages of reconciliation. The simulations were designed to mimic realistic conditions, including imperfect detectors and noisy quantum channels, to ensure the results are relevant to practical QKD systems.
Classical key reconciliation introduces vulnerabilities to quantum key distribution systems
Quantum key distribution promised unbreakable communications, but this reveals a key vulnerability hidden within the very systems designed to secure the exchange. While the quantum mechanics underpinning key exchange remain sound, the classical processing that follows, specifically key reconciliation, introduces a potential weak point exploited by this new attack. The findings demonstrate a concerning ability to shrink the search space for the correct key, potentially achieving full recovery in certain scenarios, though simulations focused solely on BB84 and Cascade protocols. The initial promise of QKD stemmed from its reliance on the laws of physics to guarantee security, rather than the computational complexity of mathematical algorithms. However, this research underscores the importance of considering the entire system, including the classical components, when assessing security. The classical post-processing stage, which includes error correction and privacy amplification, is often overlooked in security analyses. Privacy amplification is a technique used to reduce the information an eavesdropper might have gained about the key during the quantum transmission and reconciliation phases. However, if the reconciliation protocol itself is vulnerable, privacy amplification may not be sufficient to guarantee security. The attack highlights that vulnerabilities aren’t necessarily within the quantum exchange itself, but within the classical processing afterwards. Vulnerabilities in quantum key distribution extend beyond the quantum transmission itself, residing within the classical processing of data after exchange. By introducing the attack, scientists demonstrated how an adversary can exploit parity-leakage during key reconciliation, a process where errors are corrected; parity refers to whether the number of errors is even or odd. Parity-based reconciliation, a common technique, inadvertently leaks information an attacker can exploit, representing a previously unaddressed risk. Future research should focus on developing reconciliation protocols that are less susceptible to parity-leakage attacks, perhaps by employing techniques such as masking or using different error-correction codes. Furthermore, a comprehensive security analysis of QKD systems should consider the entire system, from the quantum channel to the classical post-processing, to identify and mitigate potential vulnerabilities. The implications of this work extend beyond the specific BB84 and Cascade protocols studied; it suggests that any QKD system relying on parity-based reconciliation may be vulnerable to similar attacks.
This research revealed a new attack, termed ‘Manipulate-and-Observe’, which exploits parity-leakage during the reconciliation phase of quantum key distribution. The study demonstrates that an adversary can intercept up to 11 percent of qubits and use leaked parity information to significantly reduce the security of key exchange, potentially recovering the full key. This highlights that vulnerabilities in quantum key distribution are not limited to the quantum transmission itself, but can also exist within the classical post-processing steps. The authors suggest future work should focus on developing reconciliation protocols that minimise parity-leakage to improve security.
👉 More information
🗞 The Manipulate-and-Observe Attack on Quantum Key Distribution
🧠 ArXiv: https://arxiv.org/abs/2603.29669