Vietnamese software engineer Nguyen Xuan Dong has secured patent-pending status for VRadar, a cloud-native Security Operations Center (SOC) platform designed with a post-quantum cryptographic system to protect sensitive data from future decryption threats. Developed entirely by Dong over eight months with the aid of artificial intelligence, VRadar implements NIST-standardized post-quantum algorithms in production, addressing the emerging risk of “Harvest Now, Decrypt Later” attacks. The platform processed 1.35 million real security alerts over 34 days with a 91% autonomous resolution rate, demonstrating its ability to function as a fully operational SOC. “People assume a platform this complex requires a team of 10-20 engineers,” said Dong, “I built it alone by working with AI as my development partner—not replacing engineering judgment, but accelerating the execution.”
AI-Augmented Development Builds Full-Stack SOC Platform
A lone developer has constructed a complete Security Operations Center platform, leveraging artificial intelligence to overcome the resource constraints typically associated with such complex systems. Nguyen Xuan Dong, a Vietnamese software engineer and cybersecurity researcher, built VRadar, a cloud-native SOC platform with over 150 features, in just eight months, a feat accomplished without a traditional development team. The platform’s architecture includes 41 backend modules, five AI agents, multi-tenant support, and four integrated payment gateways, demonstrating the potential of AI-augmented development. VRadar has secured patent-pending status (Application No. 1-2026-02438) for its post-quantum cryptographic secure log transport system, positioning it as an early adopter of NIST-standardized post-quantum algorithms in a production environment. This addresses the emerging threat of “Harvest Now, Decrypt Later” attacks, where adversaries stockpile encrypted data for future decryption using quantum computers.
Five specialized AI agents, including an AI Operator for alert triage and an AI Optimizer for flood detection, work independently to maintain security and provide customer support. VRadar is now targeting the underserved small and medium-sized businesses in Southeast Asia, offering SOC capabilities starting at 25 per device per month, a significant reduction from the typical 3,000-15,000 monthly cost of traditional services.
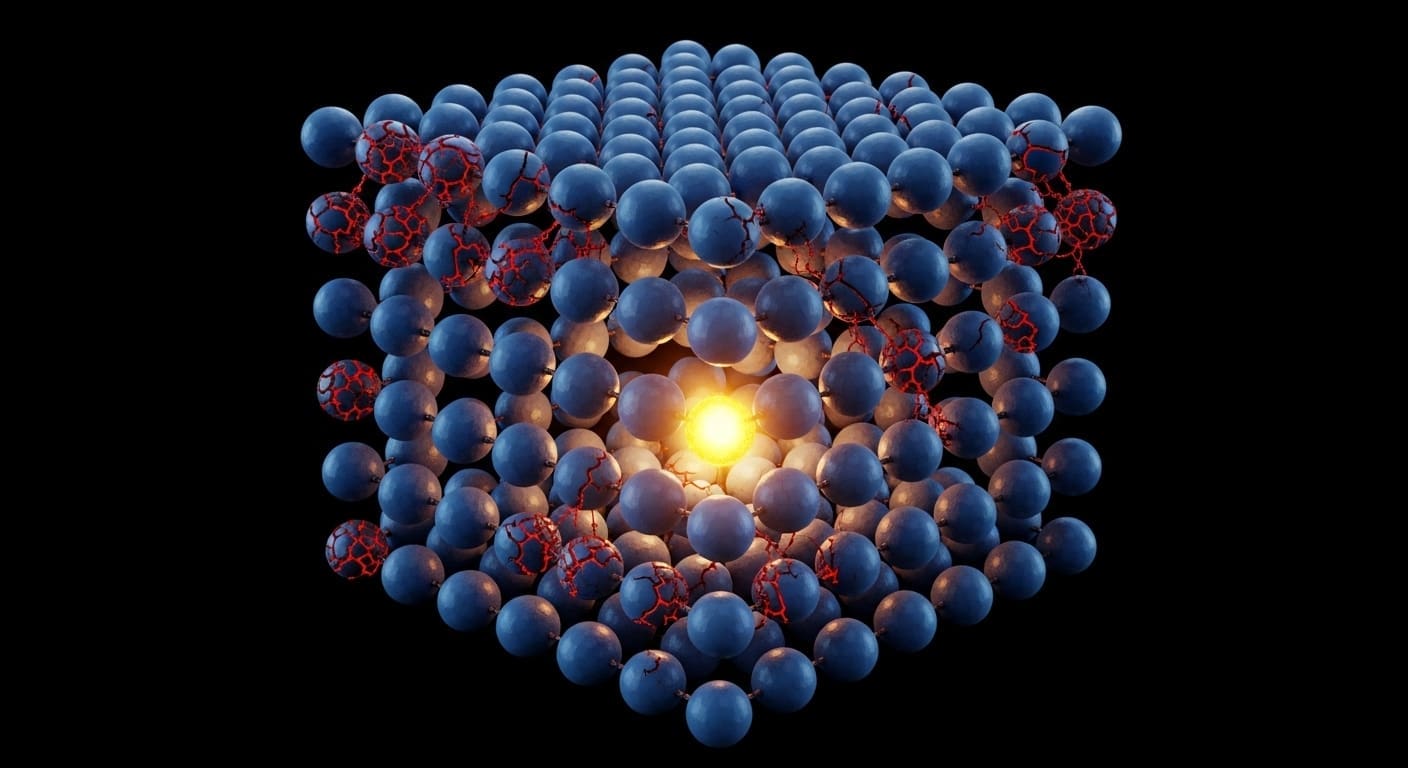
ML-KEM-768 & ML-DSA-65 Secure Log Transport System
VRadar Security has implemented a novel approach to safeguarding sensitive data with a secure log transport system leveraging post-quantum cryptography, a proactive measure against evolving threats to data security. The platform utilizes ML-KEM-768 (FIPS 203) for key exchange and ML-DSA-65 (FIPS 204) for digital signatures, technologies designed to withstand decryption attempts by future quantum computers, coupled with AES-256-GCM encryption and quantum random number generation sourced from the Australian National University’s quantum optics laboratory.
The urgency of this approach stems from impending regulatory shifts; the U.S. mandates post-quantum migration by 2035, while the EU aims for 2030, leaving organizations reliant on classical encryption vulnerable to both compliance issues and security breaches. Nguyen Xuan Dong, founder of VRadar Security, explained that “Security logs contain the most sensitive operational data a company has — authentication events, network connections, system vulnerabilities.” He added that if this data is intercepted today using classical encryption, a sufficiently powerful quantum computer could decrypt it within the next decade, and VRadar protects against that scenario now, not after the threat materializes. The company’s patent application, number 1-2026-02438, formally recognizes this innovative system. Dong’s development of this system, alongside the entire VRadar platform, is notable for its efficiency; he built 41 backend modules, five AI agents, and a multi-tenant architecture as a solo developer over eight months.
Security logs contain the most sensitive operational data a company has – authentication events, network connections, system vulnerabilities.