The convergence of sensing and communication is rapidly reshaping wireless networks, promising a future where systems not only transmit data but also perceive and understand their surroundings. Chandra Thapa and Surya Nepal, both of CSIRO Data61, alongside their colleagues, have addressed a critical need for a unified understanding of security challenges within this emerging field, known as Integrated Sensing and Communication (ISAC). Their research presents a comprehensive framework that systematically categorises threats, vulnerabilities, and defence mechanisms across all layers of an ISAC system. This work distinguishes itself from previous surveys by integrating multiple dimensions of security, revealing connections between attack vectors and potential countermeasures. By offering a detailed taxonomy and highlighting key research gaps, the authors provide an essential resource for both developers and policymakers navigating the complexities of secure perceptive networks.
ISAC Security Threats and Physical Layer Vulnerabilities The
Integrated Sensing and Communication (ISAC) is an emerging field for 6G networks, combining communication and sensing functionalities within a single wireless system. This enables applications such as environmental monitoring and enhanced localization, but also introduces new potential attack surfaces. Security and privacy are significant challenges, demanding a proactive and comprehensive approach to ensure ISAC’s full potential is realised. Physical layer attacks are a major concern, including eavesdropping, jamming, spoofing, and compromised physical layer authentication. Privacy is also at risk through precise location tracking and potential data leakage, with challenges in applying differential privacy to correlated datasets.
Traditional cybersecurity threats are exacerbated by ISAC’s unique characteristics, alongside new risks introduced by integrating Generative AI and the security of surrounding ecosystems, such as those for humanoid robots. Technologies like Reconfigurable Intelligent Surfaces (RIS) are being explored to enhance security by controlling signal propagation and mitigating interference. Researchers are also investigating physical layer security techniques, such as signal scrambling and waveform design, alongside robust authentication methods and privacy-enhancing technologies. Secure resource allocation is also being optimised to improve both security and system robustness.
Further research is needed to ensure robustness against adversarial attacks and to develop methods for preserving privacy in sensing data. Standardization of security protocols and integration of security into the entire ISAC stack are also crucial. Tailoring security solutions to specific applications, such as vehicular networks and UAVs, will be essential for effective implementation.
ISAC Security Taxonomy and Threat Landscape
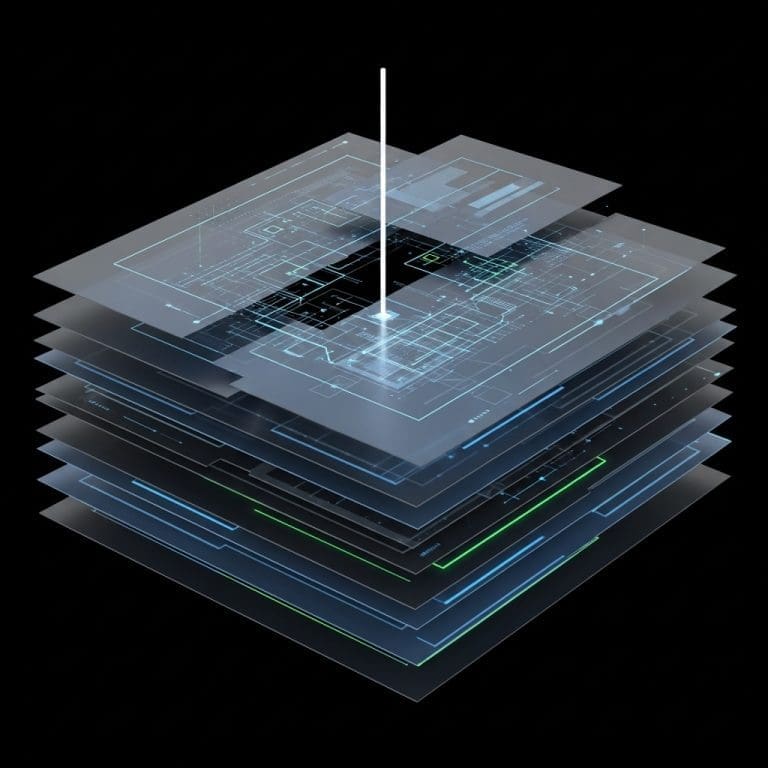
Research has detailed a systematic review of Integrated Sensing and Communication (ISAC) security, a crucial element in the development of 6G wireless networks. This work constructed a detailed taxonomic framework encompassing the entire ISAC security domain, moving beyond isolated component analysis to identify and categorise threats at the design, physical, computational, and architectural levels. The study adopted a multi-dimensional approach to security assessment, extending beyond traditional cybersecurity to address the unique challenges of ISAC’s perception-centric nature. Defence mechanisms were classified according to their deployment layer, providing a nuanced understanding of security implementation strategies.
Researchers also examined security-performance trade-offs, establishing theoretical bounds to optimise system design and functionality, with detailed consideration of sector-specific security demands. A novel classification scheme revealed previously hidden relationships between potential threats and defensive measures. The research analysed three levels of ISAC sophistication , spectrum sharing, hardware sharing, and waveform sharing , to pinpoint vulnerabilities specific to each integration level. This extended to emerging issues such as quantum resilience, AI-hardening techniques, and user privacy preservation. This approach enables a structured comparison between traditional cybersecurity and the cyber-physical security paradigm required for ISAC. By identifying key research gaps, the study delivers a foundational reference for researchers and policymakers, facilitating the development of resilient and trustworthy ISAC infrastructure.
ISAC Attack Vectors and Rapid Propagation
Scientists have established a comprehensive taxonomic framework for understanding security within Integrated Sensing and Communication (ISAC) systems. The research details four distinct propagation methods for attacks, revealing how vulnerabilities can rapidly escalate from initial compromise to significant consequences, with error propagation across layers occurring in as little as a few seconds. Data shows that horizontal propagation, particularly in Vehicle-to-Everything (V2X) networks, can trigger cascading events. A single spoofing attack on one vehicle can lead to a catastrophic emergency braking scenario affecting all connected vehicles.
Similarly, attacks on critical infrastructure, such as smart grids, can induce widespread instability and impact dependent communication and Internet of Things (IoT) devices. Temporal propagation, achieved through data poisoning in AI training pipelines, can remain latent for hours or months before malicious logic is activated. Vulnerabilities were classified into four hierarchical levels, beginning with fundamental design choices. The use of standardized waveforms, such as OFDM, inherently creates vulnerabilities to spoofing and deceptive jamming attacks. Architectural vulnerabilities were also identified; a Monostatic Architecture, with its co-located transmitter and receiver, experiences significant self-interference, potentially allowing adversaries to inject false targets undetected.
Further analysis revealed physical-layer vulnerabilities, specifically Side-Lobe Leakage in analog phase-shift beamforming, creating unintended eavesdropping zones. Beam squint effects in wide-band OFDM systems expand these zones and degrade both communication capacity and sensing accuracy. Finally, compromised programmable intelligent surfaces, termed Malicious/Illegal RIS (IRIS) Injection, can enable signal leakage or active interference, offering a foundation for developing secure ISAC systems and establishing robust security standards.
ISAC Security Threats and Defence Strategies
The integration of Integrated Sensing and Communication (ISAC) is reshaping perceptive networks and charting the course for sixth-generation (6G) technologies. This work presents a detailed framework to classify and examine the complete range of security challenges inherent in ISAC systems, systematically cataloguing potential threats and vulnerabilities across design, physical, computational, and architectural levels. The research proposes a defence-in-depth strategy built upon four interconnected pillars: physical, environmental, intelligence, and architectural security. Successfully deploying trustworthy ISAC systems necessitates a careful balance between security and performance, alongside addressing emerging concerns such as the certified robustness of radio frequency signals against adversarial attacks, quantum resilience, and the preservation of user privacy. Achieving practical implementation requires ongoing investigation into the trade-offs between security enhancements and system performance. Future research directions include further exploration of resilience against sophisticated attacks and the development of robust privacy-preserving techniques tailored to the unique characteristics of ISAC, providing a foundational reference point for securing the next generation of perceptive networks.
👉 More information
🗞 Security in the Era of Perceptive Networks: A Comprehensive Taxonomic Framework for Integrated Sensing and Communication Security
🧠 ArXiv: https://arxiv.org/abs/2601.01455