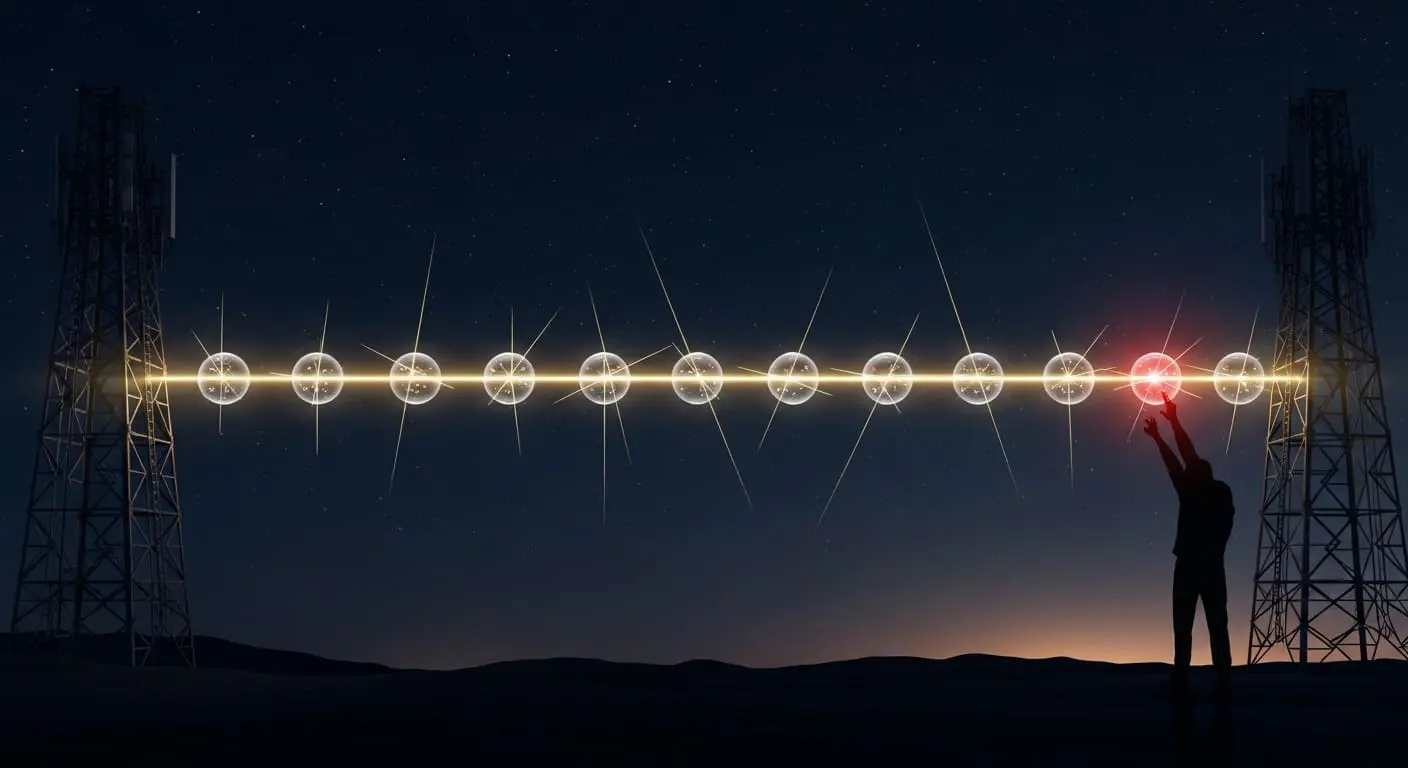
Researchers at the AIT Austrian Institute of Technology, led by Margherita Cozzolino, have developed a new topology-hiding connectivity assurance protocol for quantum key distribution (QKD) networks, addressing a critical vulnerability stemming from the dependence on trusted repeaters. The protocol empowers network providers to demonstrate a secure connection between endpoints without disclosing sensitive internal network details, thereby bolstering trust and facilitating collaboration. Advancing graph-signature techniques for multi-graphs and hidden endpoints provides zero-knowledge proofs of connectivity, supporting applications such as multi-path QKD scenarios and verifiable, privacy-preserving inter-network connections.
Zero-knowledge proofs now quantify secure network links via limited hop verification
Connectivity assurance protocols now certify connections with “at most l hops”, representing a significant improvement over previous methods reliant on fully trusted repeaters which offered no such quantifiable guarantee. This threshold, denoting the maximum permitted network hops, is fundamental for establishing secure communication links and provides a measurable metric for security. Previously, verifying connectivity without revealing network topology was considered an intractable problem in the context of QKD networks. The new protocol extends graph-signature techniques, initially designed for simpler network topologies, to accommodate complex multi-graphs, networks with multiple connections between nodes, and hidden endpoints, effectively obscuring the ultimate destination and intermediate nodes. Graph signatures are mathematical representations of a network’s structure, allowing for verification of properties without revealing the complete graph itself.
Enabling zero-knowledge proofs allows network providers to jointly demonstrate the existence of a secure connection between endpoints without disclosing commercially sensitive internal details, fostering trust and enabling collaboration between different network operators. This is particularly important in scenarios where multiple providers need to establish secure communication channels without revealing their infrastructure to competitors. The system can certify multiple disjoint paths, supporting multi-path QKD scenarios where data is split across several routes to increase security and resilience against attacks. This redundancy enhances the overall robustness of the QKD network. Joint confirmation of a secure connection, without revealing sensitive internal network details, is now possible thanks to this advancement, paving the way for more complex and interconnected quantum communication systems. Path lengths are strategically padded with loops, artificially added connections, to obscure the true number of hops within each network, further enhancing privacy and security by making it more difficult for an adversary to accurately determine the network’s structure and potential vulnerabilities. The addition of these loops introduces ambiguity, increasing the computational complexity for any attempt to deduce the actual path length.
Demonstrating quantum network connectivity whilst preserving infrastructure confidentiality
Quantum key distribution promises information-theoretic security, meaning its security is based on the laws of physics rather than computational assumptions, offering the potential for unhackable communications. However, building nationwide or even metropolitan-scale QKD networks demands more than just secure links; it requires verifiable trust between those operating the infrastructure. Current QKD systems often rely on trusted nodes, which are vulnerable to compromise, or trusted repeaters to extend the range of the quantum signal. A key step towards scalable quantum networks is now possible with this new protocol, offering a way to prove connectivity without revealing sensitive network layouts, thereby mitigating the risks associated with trusted components. Margherita Cozzolino at AIT Austrian Institute of Technology acknowledges a reliance on established number-theoretic assumptions, specifically, the hardness of certain mathematical problems, underpinning the protocol’s security, raising legitimate questions about its long-term durability against potential advances in computing, such as the development of quantum computers capable of breaking these assumptions.
Sensible caution is demonstrated by acknowledging this reliance on existing mathematical assumptions, a common practice in cryptography. While QKD itself offers information-theoretic security, the supporting protocols, like this connectivity assurance protocol, often rely on computational hardness. This method addresses the critical need for verifiable trust by allowing network operators to prove connections exist without revealing how those connections are made, a vital step for larger, more complex systems and the integration of multiple QKD networks. It moves beyond reliance on potentially vulnerable intermediary devices, offering a pathway towards scalable and auditable quantum communication infrastructure. The ability to verify truth, in this case, the existence of a secure connection, without revealing how it is known is particularly striking for complex network scenarios, offering a significant advantage over traditional methods. The protocol’s application extends beyond simple point-to-point connections; it can be used to verify the connectivity of entire sub-networks, enabling the creation of more robust and resilient quantum communication networks. Furthermore, the protocol facilitates the development of inter-network connections, allowing different QKD networks to securely communicate with each other, a crucial step towards a global quantum internet. The use of graph signatures allows for efficient verification, reducing the computational burden on network operators and enabling real-time connectivity assurance.
The researchers developed a new protocol to verify secure connections within quantum key distribution (QKD) networks without revealing the network’s internal structure. This is important because current QKD systems often rely on trusted repeaters, which could be vulnerable to attack. The protocol utilises graph-signature techniques to provide zero-knowledge proofs of connectivity, assuring both security and privacy. The authors suggest this approach can certify multiple, independent pathways, supporting more complex QKD scenarios and enabling connections between separate networks.
👉 More information
🗞 Topology-Hiding Connectivity-Assurance for QKD Inter-Networking
🧠 ArXiv: https://arxiv.org/abs/2604.01876