Researchers at MIT have developed a new security protocol that leverages the quantum properties of light to guarantee the security of data sent to and from cloud servers during deep-learning computations. This innovation addresses a significant concern in fields like healthcare, where hospitals may be hesitant to use AI tools due to privacy concerns. The protocol, which maintains 96 percent accuracy, exploits the fundamental principles of quantum mechanics, making it impossible for attackers to copy or intercept information without detection.
Led by Kfir Sulimany, an MIT postdoc, and Dirk Englund, a professor in Electrical Engineering and Computer Science, the team’s work combines techniques from deep learning and quantum key distribution to add a security layer while allowing for realistic implementation. Companies like OpenAI, which spent years and millions of dollars building proprietary models, can also benefit from this protocol. The researchers plan to study its application to federated learning and quantum operations in the future.
Secure Data Transmission in Cloud-Based Computation: A Quantum Approach
The increasing reliance on cloud-based servers for deep-learning computations has raised significant security concerns, particularly in fields like healthcare where confidential patient data is involved. To address this issue, researchers at MIT have developed a novel security protocol that leverages the quantum properties of light to guarantee secure data transmission during deep-learning computations.
The No-Cloning Principle: A Quantum Advantage
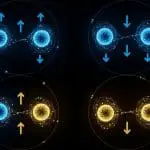
In digital computation, a malicious actor can easily copy data sent from the server or client. However, in quantum information, this is not possible due to the no-cloning principle, which states that an arbitrary quantum state cannot be perfectly copied. This property forms the basis of the researchers’ security protocol.
The Security Protocol: Encoding Weights into Optical Fields
In the proposed protocol, the server encodes the weights of a deep neural network into an optical field using laser light. The client receives this encoded information and performs operations to obtain a result based on their private data, which remains shielded from the server. The security protocol allows the client to measure only one result, preventing them from copying the weights due to the quantum nature of light.
Error Detection and Security Checks
When the client feeds the first result into the next layer, the protocol is designed to cancel out the first layer, ensuring that the client cannot learn anything else about the model. The residual light sent back to the server contains tiny errors introduced by the client’s measurement, which can be detected by the server to determine if any information was leaked.
Practical Implementation and Results
The researchers’ approach does not require special hardware, as modern telecommunications equipment already incorporates optical lasers that can be used for encoding data into light. In their experiments, they found that their protocol could guarantee security for both server and client while enabling the deep neural network to achieve 96% accuracy.
Future Directions: Federated Learning and Quantum Operations
The researchers plan to explore how this protocol can be applied to federated learning, where multiple parties use their data to train a central deep-learning model. They also aim to study its application in quantum operations, which could provide advantages in both accuracy and security.
The Significance of This Work: Combining Deep Learning and Quantum Key Distribution
This research combines techniques from deep learning and quantum key distribution in a novel way, adding a security layer to the former while allowing for realistic implementation. As Eleni Diamanti, a CNRS research director at Sorbonne University, notes, “This work can be interesting for preserving privacy in distributed architectures.” The practical realization of this protocol could have significant implications for secure data transmission in cloud-based computation.
This work was supported, in part, by the Israeli Council for Higher Education and the Zuckerman STEM Leadership Program.
External Link: Click Here For More