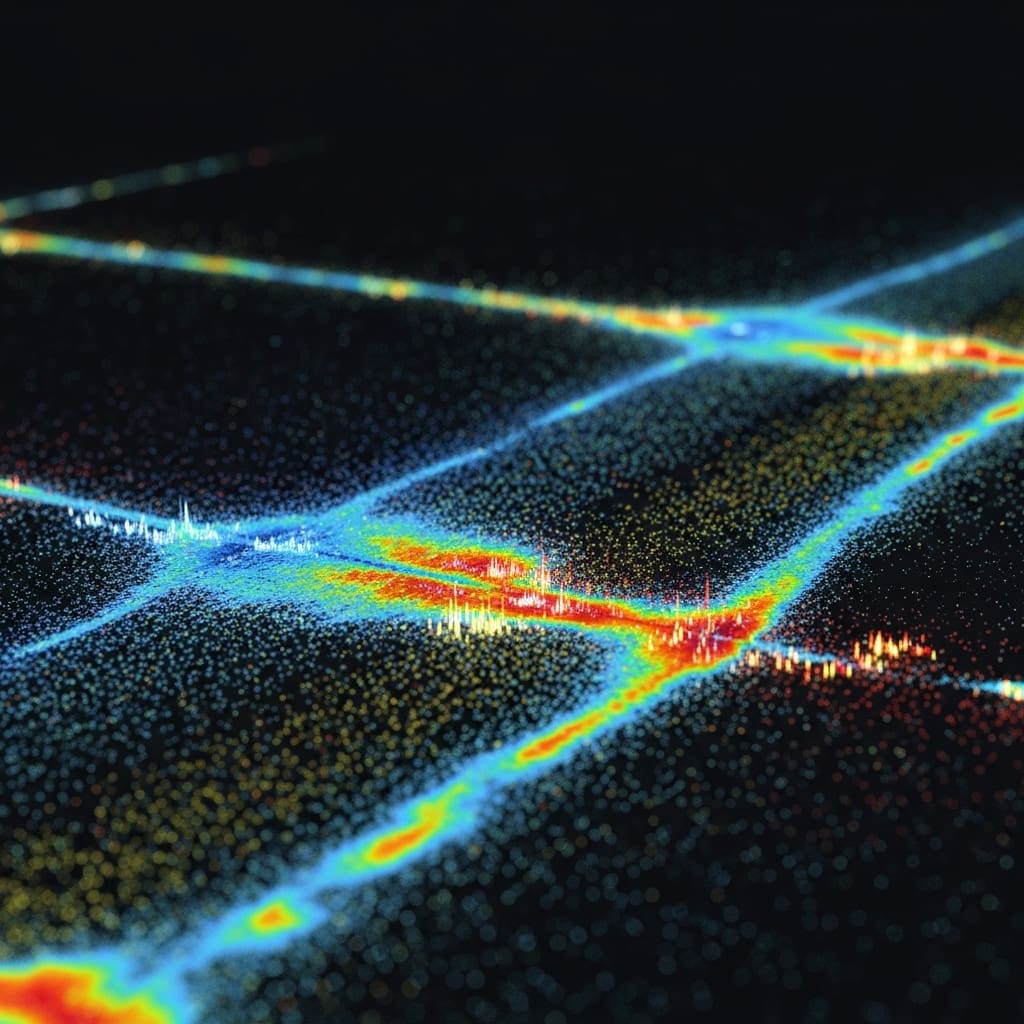
Memory safety bugs in GPU programs represent a significant threat to the security and dependability of increasingly popular GPU-accelerated applications. Researchers Anubhab Ghosh, Ajay Nayak, and Dhananjay Rao Thallikar Shyam, all from the Indian Institute of Science, alongside Arkaprava Basu et al., demonstrate the existence of previously undetected, input-dependent out-of-bounds (OOB) errors that current runtime detection tools fail to identify. This research is significant because it reveals a blind spot in existing GPU debugging methodologies, particularly concerning OOBs triggered only by specific inputs and those arising from logical partitioning within memory allocations. To address this, the team developed SCuBA, a novel compile-time technique that leverages semantic analysis of both CPU and GPU code to proactively identify potential memory errors, achieving complete detection of elusive bugs across a benchmark of 20 programs where existing tools, such as Compute Sanitizer, fall short.
Detecting elusive GPU out-of-bounds accesses statically
The team achieved a significant advancement by moving beyond runtime detection, which inherently requires a bug to manifest during execution, and instead focusing on compile-time analysis to proactively identify potential vulnerabilities. The study unveils that many CUDA programs logically partition a single memory allocation into multiple data structures, creating opportunities for intra-allocation OOBs when instructions access the wrong data structure within that allocation. SCuBA addresses this by tracking logical partitioning within GPU code, enhancing its ability to pinpoint these subtle errors. The absence of such a relationship signals a potential OOB, even without knowing the specific input data.
The work opens new avenues for enhancing the security and reliability of GPU-accelerated software, particularly in critical applications like artificial intelligence, machine learning, and high-performance computing. By identifying elusive bugs during compilation, SCuBA eliminates the need for runtime overhead and the reliance on ‘lucky’ inputs to trigger bug manifestation. This proactive approach promises to significantly reduce the risk of security vulnerabilities and intermittent failures in production deployments, offering a substantial improvement over existing memory safety tools.
Scientists Method
Scientists identified a critical gap in GPU memory safety testing, revealing that input-dependent out-of-bound (OOB) accesses routinely evade existing detection tools. Researchers discovered these elusive bugs manifest only under specific inputs, a characteristic that renders runtime-based detection techniques ineffective. Experiments employed a detailed analysis of CUDA programs, focusing on how allocation sizes are determined in CPU code and how offsets are calculated in GPU code. This analysis enabled the construction of constraints representing the relationships between these variables, forming the basis for the SAT solver’s verification process.
Researchers implemented a rigorous methodology to validate SCuBA’s effectiveness. The study compared SCuBA’s performance against Compute Sanitizer, a state-of-the-art runtime tool, across 20 programs. The technique reveals the presence of input-dependent OOBs in widely used open-source CUDA programs, such as a fluid advection simulation from HeCBench, where 19 such bugs were identified. To illustrate, the team analysed a kernel within the fluid simulation program, pinpointing an OOB access on line 4 where a thread reads from a global memory array, cubD, using an index id. The size of cubD is determined by input parameters cubN and Nelements in the host code, establishing a semantic relation crucial for SCuBA’s analysis. This approach enables the detection of OOBs that would otherwise remain hidden during testing, significantly enhancing the reliability of GPU-accelerated software.
Input-dependent GPU out-of-bounds errors uncovered a critical rendering
Scientists have uncovered input-dependent out-of-bounds (OOB) errors in real-world GPU programs that existing detection tools miss. Experiments revealed tens of such input-dependent OOBs within open-source CUDA programs and popular libraries, highlighting a significant vulnerability in GPU-accelerated software. These OOBs remain hidden from current techniques because they do not consistently appear during program execution. SCuBA, a Static analysis tool, operates at compile time, eliminating the need for runtime overhead and hardware modifications. Researchers discovered a new type of bug, intra-allocation OOBs, which occur when a program logically partitions a single memory allocation into multiple data structures.
Tests prove that current techniques are unable to detect these intra-allocation OOBs as they only track allocation boundaries and ignore internal partitioning. The work establishes that the presence or absence of these semantic relations is key to identifying potential OOBs. Measurements confirm that SCuBA can accurately identify potential OOBs without requiring program execution or specific inputs. Data shows that SCuBA’s approach, based on inferring semantic relations, offers a significant improvement over runtime-based methods. This research opens avenues for building more secure and reliable GPU-accelerated applications, particularly in domains like artificial intelligence, machine learning, and high-performance computing.
SCuBA detects input-dependent GPU memory errors
Scientists have identified a critical vulnerability in GPU-accelerated software stemming from input-dependent out-of-bounds (OOB) memory accesses. Existing detection tools, reliant on runtime analysis, fail to identify these bugs because they only manifest under specific input conditions. Researchers also discovered intra-allocation OOBs, occurring when logically partitioned memory allocations are improperly accessed, a scenario overlooked by current techniques. This work introduces SCuBA, a novel compile-time technique designed to address these limitations. Furthermore, it analyses GPU code to identify and prevent intra-allocation OOBs through tracking of logical memory partitioning.
The findings establish that static analysis, focusing on semantic relationships between variables, can effectively detect input-dependent OOBs in GPU programs. Authors acknowledge that SCuBA’s current implementation focuses on a specific set of programs and may require further optimisation for broader applicability. Future research directions include extending SCuBA to support a wider range of GPU programming models and exploring integration with existing compiler infrastructure to facilitate wider adoption.
👉 More information
🗞 Chasing Elusive Memory Bugs in GPU Programs
🧠 ArXiv: https://arxiv.org/abs/2601.21552