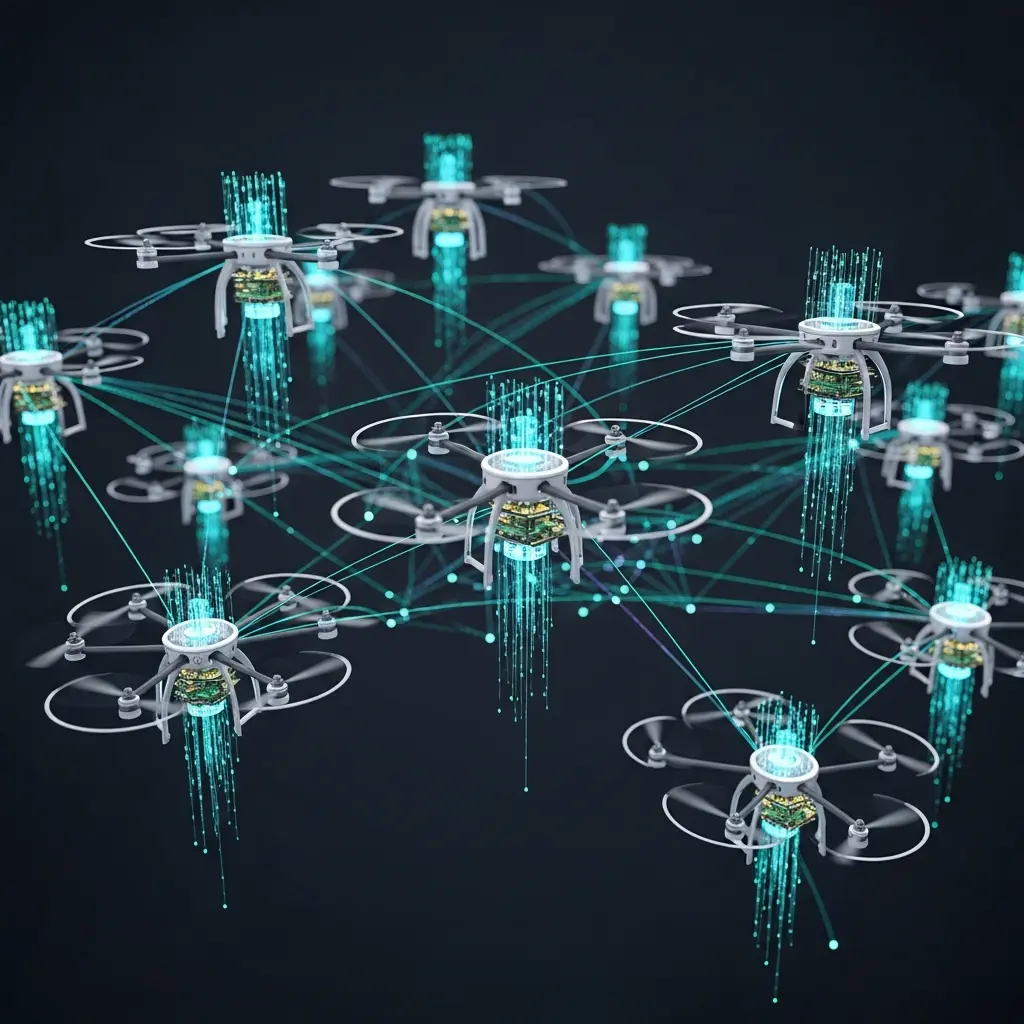
Researchers investigate dual-unmanned aerial vehicle (UAV) networks to enhance secure communication, deploying one UAV for data transmission to ground users and a second for jamming hostile eavesdropping attempts. Xinran Wang from Wuhan University, Peng Wu from Wuhan University, and Xiaopeng Yuan from RWTH Aachen University, along with Yulin Hu and Anke Schmeink, demonstrate a novel approach to maximise minimum secrecy throughput across all users by optimising UAV trajectories and communication scheduling simultaneously. This work is significant because it tackles the complexities of continuous UAV movement and the interplay between transmitter and jammer, ultimately reducing the problem to a manageable, finite form without compromising performance. Through characterising optimal trajectories as a collaborative successive hover-and-fly structure, the team achieves improved secrecy and fairness with substantially reduced computational demands, as evidenced by numerical comparisons with existing methods.
This work addresses the challenge of delivering confidential data from one UAV to multiple ground users while simultaneously employing a second cooperative UAV to actively jam potential eavesdropping attempts.
The core innovation lies in a newly characterised trajectory structure, termed collaborative successive hover-and-fly (co-SHF), which governs the movement of both UAVs. This co-SHF structure dictates that the UAVs synchronise at limited co-hovering points, with at least one UAV maintaining maximum speed during flight segments.
By rigorously proving the optimality of this co-SHF structure, the researchers have successfully reformulated a complex, infinite-dimensional problem into a manageable, finite-dimensional one. The optimisation now focuses on hovering and turning points, hovering durations, and communication scheduling, rather than continuous-time trajectories.
To further simplify calculations, a minimum-distance approximation of anti-collision constraints was adopted, alongside concave lower bounds on secrecy throughput within a successive convex approximation (SCA) method. This combination ensures both convergence and reduced computational complexity, a critical advancement for real-time applications.
Numerical results demonstrate substantial performance gains with the proposed co-SHF design when compared to traditional time-discretisation methods and systems without jamming. The new approach not only enhances minimum secrecy throughput and user fairness but also achieves these improvements with significantly less processing time.
This breakthrough paves the way for more efficient and secure UAV communication networks, particularly relevant for future 6G wireless infrastructures and applications requiring robust data protection. The ability to optimise trajectories and scheduling in a computationally efficient manner unlocks possibilities for dynamic, adaptive, and highly secure aerial communication systems.
UAV trajectory and scheduling optimisation via co-SHF structure and finite-dimensional reformulation enables efficient airspace management
A collaborative successive hover-and-fly (co-SHF) structure underpins the methodology for optimizing dual-unmanned aerial vehicle (UAV) jamming-aided secure communication networks. The research focuses on maximizing minimum secrecy throughput across ground users (GUs) by jointly designing UAV trajectories and communication scheduling, with one UAV delivering data and another providing jamming against a ground eavesdropper.
Initial work characterized the optimal trajectories, rigorously proving their adherence to the co-SHF structure where UAVs visit synchronized co-hovering point pairs and maintain maximum speed during flight segments. This co-SHF structure enabled reformulation of the original problem into a finite-dimensional form, optimizing over hovering and turning points, hovering durations, and scheduling assignments without sacrificing optimality.
To manage the complexity of continuous anti-collision constraints, a minimum-distance approximation was adopted, simplifying the calculations while maintaining accuracy. Secrecy throughput was further refined using concave lower bounds within a successive convex approximation (SCA) method, ensuring convergence and reducing computational demands.
The SCA method, combined with the co-SHF reduction in optimization variables, significantly lowered the complexity of the optimization process. Performance was evaluated by comparing the proposed co-SHF design against time-discretization benchmarks and a scenario with no jamming, demonstrating improvements in both minimum secrecy throughput and user fairness.
Numerical results consistently showed that the co-SHF approach achieved superior performance with substantially reduced runtime compared to alternative methods. This methodology provides a practical and efficient solution for secure communication in dynamic UAV networks.
Cooperative UAV Trajectory Optimisation via Successive Hover-and-Fly for Secure Communications is presented
Researchers developed a dual-unmanned aerial vehicle (UAV) system for secure communication, achieving improved fairness and reduced runtime compared to existing methods. The core of this work lies in a collaborative successive hover-and-fly (co-SHF) structure, rigorously proven to characterise optimal UAV trajectories.
This structure dictates that UAVs visit a limited number of synchronised co-hovering point pairs, with at least one UAV maintaining maximum speed during flight segments. The proposed co-SHF design reformulates the original problem into a finite-dimensional form, optimising over hovering and turning points, hovering durations, and scheduling without sacrificing optimality.
A minimum-distance approximation of continuous anti-collision constraints was adopted for tractability, alongside concave lower bounds on secrecy throughput within a successive convex approximation (SCA) method. This SCA method demonstrably converges and, due to the co-SHF reduction in variables and constraints, achieves low computational complexity.
Numerical results demonstrate significant performance gains with the co-SHF design. Compared to time-discretization benchmarks, the new approach improves minimum secrecy throughput and user fairness while substantially decreasing runtime. The study highlights the benefits of coordinated trajectory design in enhancing secure communication in UAV networks, offering a scalable solution that avoids the accuracy-complexity trade-offs inherent in time-discretization methods. This collaborative approach provides enhanced spatial flexibility, improving secrecy performance by separating transmission and jamming functionalities across two aerial platforms.
UAV trajectory optimisation yields gains in secure communication performance by minimizing interception risk
Researchers have developed a system utilising two unmanned aerial vehicles (UAVs) to enhance secure communication networks, with one UAV delivering data and the other providing jamming to protect against eavesdropping. The core achievement lies in maximising the minimum secrecy throughput to multiple ground users by optimising both the UAV trajectories and communication scheduling.
This was accomplished through a novel approach that characterises the optimal UAV movements, demonstrating they follow a collaborative successive hover-and-fly structure. This collaborative structure simplifies the complex, infinite-dimensional problem into a manageable, finite-dimensional one, allowing for efficient computation.
The system’s performance was validated through simulations, showing improvements in both minimum secrecy throughput and fairness compared to existing methods, while also reducing computational time. Results also highlight the importance of carefully balancing jamming power to enhance security without hindering legitimate communication.
The authors acknowledge that the current design assumes a simplified propagation model and perfect channel information. Future work could address more complex scenarios, including mobile users, multiple eavesdroppers, and imperfect channel estimation, all building upon the established collaborative hover-and-fly foundation. Furthermore, the demonstrated trajectory structure is broadly applicable to various multi-UAV networks performing coordinated tasks, suggesting potential for scalability and adaptation to diverse mission profiles.
🗞 Efficient Trajectory Design and Communication Scheduling for Dual-UAV Jamming-Aided Secure Communication Networks
🧠 ArXiv: https://arxiv.org/abs/2601.20314